Internet of things (IoT) for Oil and Gas
1. Automating Remote Operations At a time when well drilling and completion complexities are increasing and field experts are becoming scarcer, automation offers many benefits. Besides capturing domain knowledge, automation increases safety and decreases personnel time on-site and therefore lowers cost. Automation has also been proven to improve well quality, and decrease downtime and equipment failures.
2. Enabling Massive Data Collection The data generated from a single well can be sizeable; a large field of wells can produce massive amounts of valuable information. Industrial Internet technology can tackle the large-scale collection across an entire site. The proven results include better asset utilization across all wells, reduced effluents, and accelerated production. Broad oversight also accommodates hydrocarbon recovery, and offers insights that can lead to better decision making about well locations.
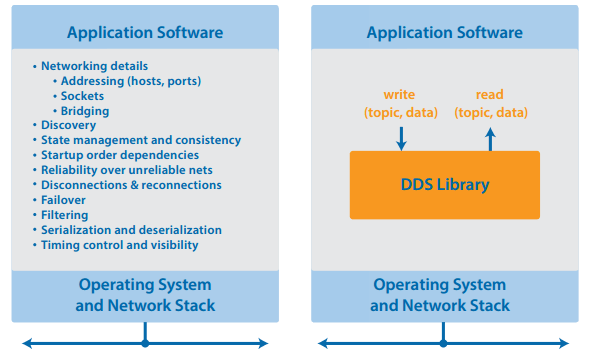
3. Integrating Analytics To fully exploit analytics, all of the components of the system under study must be integrated such that information can be reliably gathered. This is especially critical for real-time analytics that directly drive process improvements and production optimizations. The data collection topology behind large-scale analytics can be complex, however. Every smart machine within every system must be connected and data driven up to site busses and eventually into the cloud or control centers for consolidation at the application level. Using DDS across the system allows designers to build a single logical DataBus that connects the various subsystems. A single logical sensor-to-cloud DDS DataBus can hide the underlying complexities of the physical connections between machines, systems, and sites.
4. Securing Operations The recently adopted DDS security standard offers complete security protection for data flows. Data flows can be secure, independent of protocols, roles, and nodes. The DDS security model allows protection of every dataflow. This “per-topic” security is logically simple: the DataBus connects information sources to information sinks. The security model simply enforces the connections by authenticating endpoints and allowing only the configured communications. The protocol supports discovery authentication, data-centric access control, plug-in cryptography, tagging/logging, and secure multicast – in a 100%-standards-compliant manner. Because it leverages the existing data-centric design, adding security to an existing DDS system does not require any additional coding; security is implemented only by configuration. Truly robust security requires both protection (stopping unwanted activities) and detection (finding and reporting when the protection has been compromised). This is why, for instance, a typical laptop has both a firewall (protection) and a virus scanner (detection). The DDS DataBus also makes it easy to combine both protection and detection. Because it is a multi-channel bus, DDS supports facile data tapping. Because that bus has extensive information about the connection information and access to the data formats, it enables tapping programs to detect anomalies.
5. Replacing Special Software with Industrial Internet Platforms Developing distributed systems applications traditionally required a significant amount of networking and error handling logic. DDS middleware makes it possible to replace previously low-level communications programming with high-level data-centric publish/subscribe interfaces. Topics guide communications, rather than strict physical addressing schemes (sockets, host names, IP addresses, and ports).
Technologies
Tags
KEY BENEFITS
Explore how IT can help your business by
- Energy
- Border and Identity management
- Mining and Oil & Gas Extraction
- Telecommunications
- Pharmaceuticals and Healthcare
- Media and Publishing
- Chemicals
- Agriculture and Forestry
- Textile
- Electronics and High Tech
- Wholesale and Distribution
- FMCG
- Banking and Finance
- Automotive
- Insurance
- Retail
- Government and Public service
- Real Estate & Construction
- Non-Profit
- Freight, Logistics, Transportation & Warehousing
- Healthcare
- Accomodation and Food
- Construction & Engineering
- Education and Research
- Entertainment, Recreation and Arts
- Manufacturing
- Miscellaneous
- Professional and Technical Services
- Law services
- Utilities
- Travel and Tourism
- Finance and Accounting
- Human Resources
- Procurement, Supplier and Outsourcing
- Property and Facility
- Quality Improvement and Innovation
- Supply Chain, Inventory and Logistics
- Support
- Project Management and governance
- Operations
- Information Technology
- Manufacturing
- Sales and Marketing
- Improving Asset Efficiency
- Inventory
- PP&E
- Receivables & Payyables
- Increase Operating Margin
- COGS
- Income Taxes
- SG&A
- Managing Market Expectations
- Revenue Growth
- Price Realization
- Revenue Volume
- Business Intelligence
- BigData
- Enterprise Application Integration
- Internet Of Things (IoT)
- Mobile
- SharePoint
- Virtual Reality
- Web
- Collaboration
Explore how IT can help your business by
- Government and Public service
- Real Estate & Construction
- Non-Profit
- Freight, Logistics, Transportation & Warehousing
- Healthcare
- Accomodation and Food
- Construction & Engineering
- Education and Research
- Entertainment, Recreation and Arts
- Manufacturing
- Miscellaneous
- Professional and Technical Services
- Law services
- Utilities
- Travel and Tourism
Recent Blogs
Straddling these two worlds makes for a hell of a person. It’s a fire sign and ruled by the headstrong Ram, making them stand their ground and refuse to be pushed around. Conventional family values are something they strictly follow, for example https://astrozella.com/may-taurus-vs-april-taurus/. So, she will do anything within her means to ensure it clings to every chance that pops up in her career.
If that’s not enough, you can share photos on social media and do more, thanks to IFTTT. There were a ton of backpackers there on longer term trips also interested in hanging out, tons of cheap activities and cheap steak so people can do stuff together easily, and even stayed at a hostel with free wine! Because they are an active dog breed, the Vizsla needs something to keep them busy if they are left alone – like a puzzle treat box or a proper dog toy more info. It’s no surprise, but summer is peak tourism season for Kennebunk, Kennebunkport, and the surrounding area, and like most of Maine’s coastal towns, the Kennebunks turn into sleepy towns in the winter.
The cup should encompass your breast and provide a smooth transition from bra to breast, with no skin squeezing out of the top. The wings stimulate your lateral clitor. The shape of the toy and the weight of the steel do a lot of the work for you https://kinkazoid.com/male-masturbators/. A DIY pussy will help you reach the climax, but it can’t be compared to the one you can get with professional models from Spider, Meiki, Fleshlight or Rends.
For women, this can be a great way to control the amount of stimulation they’re receiving. Odette Lace Eye Mask Black. Since we’re on the topic of long term wear I’ll address the second most asked question: How do you go to the bathroom https://911cashtilpayday.com/. In case you forgot that the internet is full of pretenders and people who say they’re something or someone they aren’t, we’ll remind you again.
Physical arousal involves direct and indirect stimulation of erogenous sensory nerves. Still, it’s fair to say that none of these choices are purely aesthetic, and the Tentacle’s form does provide some amazing texture and stimulation. Variations: Dildo choices are endless, and range in size, shape, and color dildo mouth gag. With sturdy nylon straps that can hold up to 250 pounds, you and your partner can take turns swinging and turning as you experiment with multiple sex positions.